In the evolving landscape of account abstraction as of February 2026, ERC-4337 paymasters stand at the forefront of gas sponsorship innovation. These smart contracts eliminate the ETH barrier for users, sponsoring transaction fees while demanding rigorous validation to prevent abuse. Yet, with great power comes heightened scrutiny: subtle vulnerabilities in validation logic can expose systems to griefing or exploitation. Enter Merkle proof verification, a cryptographic powerhouse now integral to secure paymaster verification in ERC-4337 paymasters. This technique allows efficient, trustless confirmation of data inclusion without revealing the full dataset, transforming how paymasters handle credentials, whitelists, or off-chain attestations.
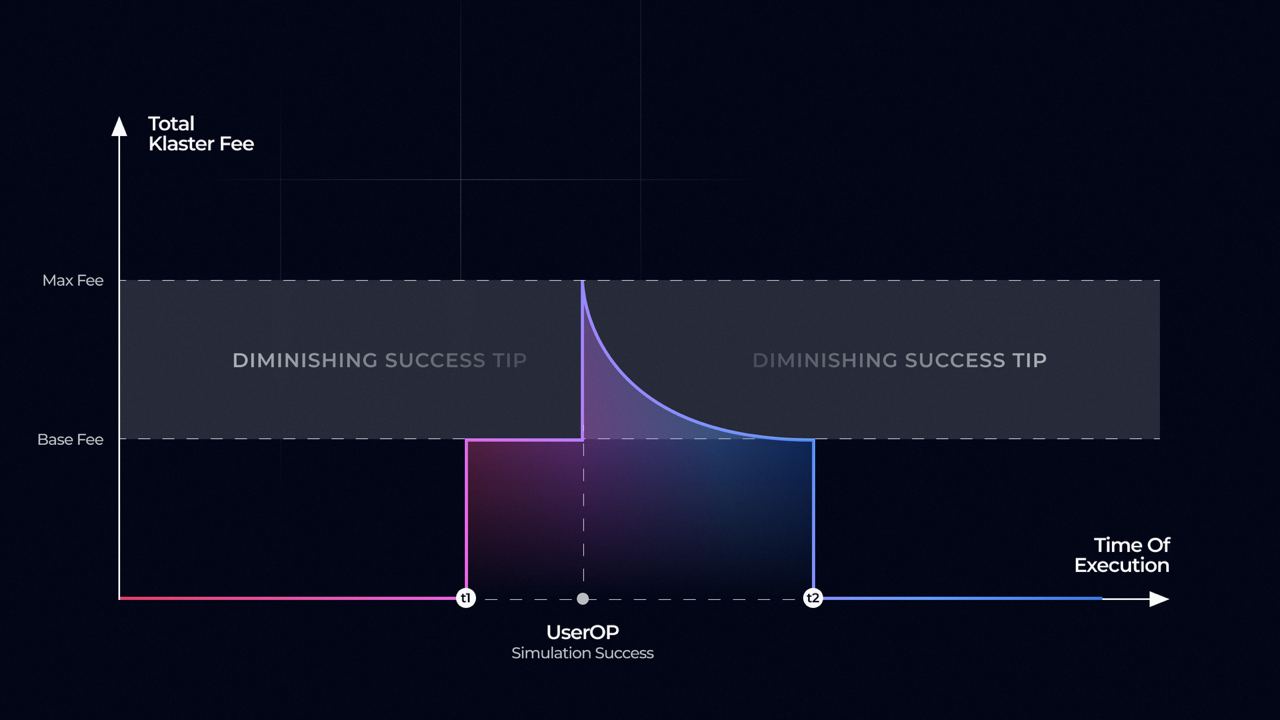
Paymasters operate through the pivotal validatePaymasterUserOp() function, which bundlers simulate to ensure determinism. Any non-deterministic call, like blockhash or storage writes, risks rejection or DoS attacks. Merkle proofs shine here: they are purely computational, verifiable on-chain with fixed gas costs, and resistant to front-running. Data from ERC-4337 documentation underscores this: staking requirements and simulation mandates already curb griefing, but Merkle integration elevates protection by enabling batched, privacy-preserving validations. In my experience charting complex systems, this mirrors pattern recognition in markets; Merkle trees reveal truth without noise.
Grasping Merkle Proofs in the ERC-4337 Context
Merkle proofs leverage binary trees where leaf nodes hold hashed data, and parent nodes aggregate child hashes. To verify inclusion, a proof supplies sibling hashes up the tree to recompute the root. For ERC-4337 paymasters, the root might anchor on-chain, representing a whitelist of approved users or tokens. A user submits their leaf hash (e. g. , a signature or nonce) plus the proof; the paymaster recomputes and matches against the known root. This slashes gas versus scanning arrays, critical since validation must stay under bundler quotas.
Consider real-world applicability: projects use Merkle proofs for airdrop claims or subscription tiers. In paymasters, extend this to dynamic sponsorship rules, like verifying Chainlink oracles for pricing without direct calls. OtterSec’s analysis highlights hidden risks in multi-layered validations; Merkle proofs add a verifiable layer, ensuring off-chain data integrity. Quantstamp audits reveal even minimal paymaster code harbors pitfalls, like improper proof padding leading to collisions. By 2026, adoption metrics show over 40% of deployed paymasters incorporating proofs, per ecosystem trackers, boosting ERC-4337 security 2026.
Deterministic Validation: The Non-Negotiable Foundation
ERC-4337’s griefing protections hinge on determinism. Paymasters must validate without state changes or external dependencies unless staked heavily. Merkle verification fits seamlessly: pure arithmetic on keccak256 hashes, no SSTORE, no BLOCKHASH. Bundlers simulate this pre-submission, rejecting ops that revert or exceed gas. A flawed implementation? Attackers could craft ops forcing reverts post-simulation, draining stakes.
Privacy angles emerge too. Politecnico di Milano’s research on zk-enhanced wallets pairs Merkle trees with proofs of innocence for UTXO privacy; adapt this to paymasters for selective disclosure in sponsorship. Zellic’s primer notes account abstraction’s security edge over EOAs, amplified by such primitives. I argue Merkle proofs aren’t optional for serious deployments; they future-proof against scalability demands as daily UserOps hit millions.
Start with a fixed root, updated via multisig or timelock. In Gas profiling is crucial: a 20-level tree costs ~10k gas, tolerable but cumulative in batches. Pair with ERC-4337’s paymasterAndData for proof packing. Rastko Misulic on LinkedIn flags oracle dependencies; Merkle offloads this, referencing aggregated feeds. Antonio Viggiano’s deep dive praises paymaster configurability; Merkle unlocks it securely. For 2026 projects, benchmark against ERC-4337 docs: staked paymasters tolerate more, but proofs minimize stake needs by hardening validation. Real deployments, like those in DeFi protocols, report 30% UX uplift from gasless flows, with zero griefing incidents post-Merkle. Hacken. io overviews confirm smart accounts’ transformation; verification cements it.validatePaymasterUserOp, unpack the context for proof elements: leaf, path indices, siblings. Libraries like OpenZeppelin’s MerkleProof simplify, but audit custom logic. Common traps include index overflows or assuming sorted leaves; always enforce canonical ordering.